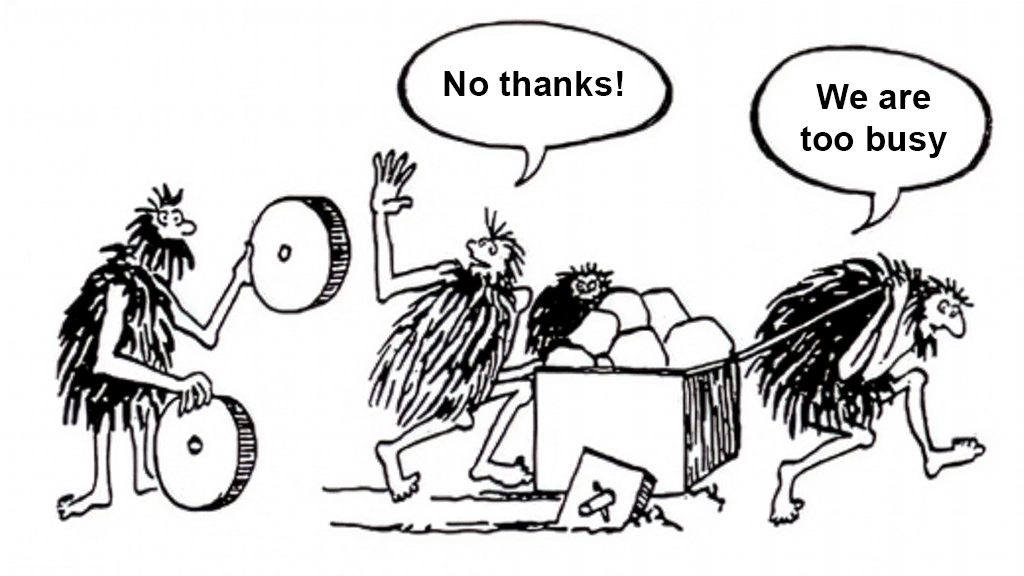
The absurdity is both humorous and painful.
Blog posts
2026
2024
Where do we go from here?
To you, the seventy plus million people. You know who you are.

2023
USPS incomplete address scam
How does the “incomplete address” scam work? What happens if you divulge your payment information? How can you avoid it?

2022
Anti-fingerprinting Configuration for NGINX
Software on the web discloses a wealth of information with little prompt. Help protect your privacy by using these anti-fingerprinting options.

2021
2020
CVE-2018-10756: Transmission
CVE-2018-10756: Transmission can crash or possibly execute arbitrary code when opening a maliciously crafted torrent file.
2019
Clean Up Your Gems
In this post, I urge Ruby gem maintainers to be aware of the files they distribute with their gems. If your gem includes files which you have not consciously included for a specific reason, please consider removing these files from your gem.
2018
Unit Price Calculator
I’m at the store shopping for groceries, and I’m considering buying a thing. I’ve narrowed down my selection to two final candidates. These two options look equivalent in nearly every aspect, except for the part where they are packaged in differently-sized containers, and the price is different. So… what now?
2016
Vizio TV - "No Signal" on HDMI ports
So you own a Vizio-brand television set. You’ve got the fancy keyboard remote and the video streaming apps right on your TV! But, when you plug in a device to any one of the HDMI ports, the TV merely displays, “No Signal”.
Rapidly Sunsetting FTP
File Transfer Protocol, or FTP, is considerably insecure and should not be used anymore. Seriously.
2015
How to Set Up a Garry's Mod Dedicated Server
After fights with the server browser and entirely too many buggy prop hunt servers, I decided to set up my own dedicated server for Garry’s Mod. Documentation for this does exist, but I had to start from scratch a few times in order to get everything just right. This is the information I wish I had when setting it up the first time.
2014
AT&T U-verse is Extremely Slow
AT&T has done it again.
My ISP is Cheating on Speed Tests, Too!
In this very inspiring blog post, Kirsle accuses Time Warner Cable in Los Angeles, CA of traffic-shaping speed tests in order to make it appear that they are delivering internet speeds as advertised (when in fact, they aren’t). My post aims to be a spin-off experiment.
How Not to Install an Operating System
I hate it when software triple-checks you before performing a potentially risky operation. Operating system install tools are especially bad about this. Sometimes, they prevent you from installing the OS altogether.
2012
Borderlands 2 Compatibility Pack Pricing
Why did the Borderlands 2 compatibility pack cost -1 MSP, and then 4,294,967,295 MSP, simultaneously?
2010
Trees
This picture was my desktop background for a very long time.